System P2P meaning
What Is a P2P System?
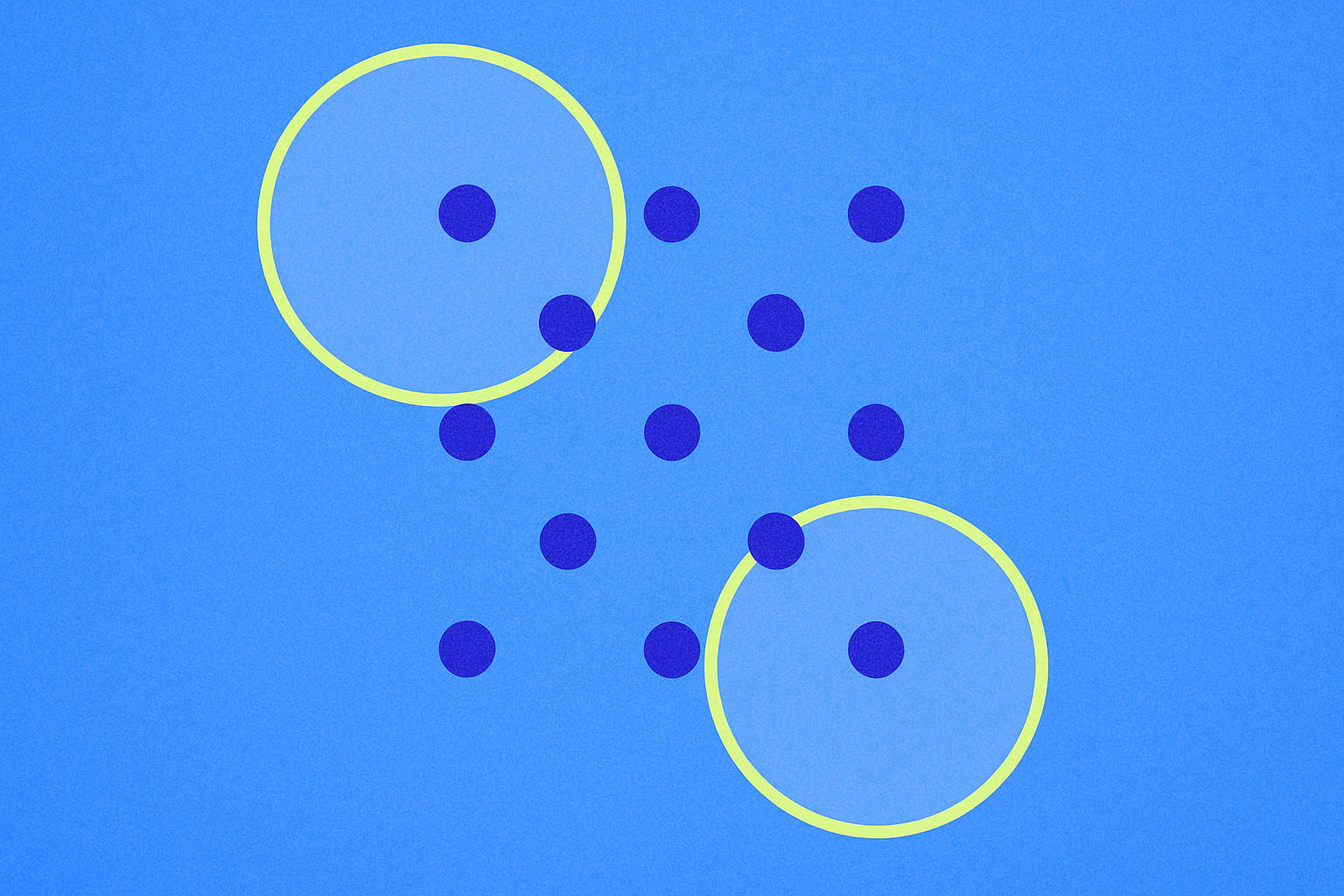
A P2P (peer-to-peer) system is a decentralized network architecture where participants connect directly to exchange data, without relying on a single central server. In this setup, each "node" refers to an individual device or application that can both receive and forward information.
Within a P2P system, the network functions much like a community of neighbors: every node helps relay messages and share resources. Common examples include the blockchain node network, BitTorrent file sharing, and peer-to-peer cryptocurrency trading.
Why Are P2P Systems Important in Blockchain?
P2P systems form the foundational network layer for blockchain operations, enabling true "decentralization"—no single entity has overarching control. Nodes broadcast transactions and blocks directly to one another, ensuring data consistency through mutual verification.
This architecture offers strong fault tolerance and resistance to censorship. Even if some nodes go offline, others can continue relaying and recording data, keeping the network operational. Additionally, the entry barrier is low—anyone can join with their own device, which boosts transparency and verifiability.
How Do P2P Systems Work?
At the core of a P2P system are node discovery and message propagation. Node discovery involves finding other nodes to connect with; message propagation refers to spreading transactions or data across neighboring nodes. Many blockchains use a "gossip protocol"—similar to word-of-mouth in a community—to disseminate information from node to node until the entire network is reached (learn more).
For more efficient resource discovery, some P2P systems use distributed indexing methods, like a "distributed phone book." Distributed Hash Tables (DHT), for instance, spread index management among nodes based on key ranges, minimizing central dependencies.
In home network environments, routers often block direct external access to your devices—known as the "NAT problem." P2P systems typically overcome this by using port mapping or relay nodes to establish stable connections between peers.
What Are the Key Use Cases for P2P Systems in Crypto?
P2P systems have broad applications in the crypto space:
- Blockchain node propagation: Bitcoin and Ethereum nodes broadcast transactions and synchronize blocks within a P2P system, efficiently collaborating so those who learn first relay first.
- Content distribution and NFT verification: P2P protocols like IPFS distribute and store metadata or files for digital collectibles without relying on a single server, enhancing availability.
- Peer-to-peer fiat trading: Gate’s P2P fiat trading allows buyers and sellers to make payments directly; the platform escrows crypto assets, releasing them only after payment is confirmed, reducing disputes and fraud risk.
- Direct wallet transfers: Users initiate transfers via their wallets; network nodes validate and forward transactions in the P2P system until miners or validators record them.
How Does a P2P System Compare to Client-Server Architecture?
The main difference between P2P systems and client-server architecture is centralization. Client-server models depend on one or more central servers for request handling, storage, and control; P2P systems distribute transmission and collaboration across all nodes.
As a result, P2P networks are more resilient—if any node goes offline, the network remains intact. However, client-server setups offer straightforward centralized management, access control, and performance tuning, making them better suited for scenarios requiring strict consistency and governance. Many real-world systems blend both models for optimal results.
What Risks Should You Consider When Using P2P Systems?
Three main risk categories in P2P systems are network, privacy, and financial risks.
Network risks include "Sybil attacks" (where many fake nodes manipulate consensus) and "eclipse attacks" (isolating target nodes among malicious peers), which can compromise information integrity or routing. Use trusted node lists, limit connection numbers, and keep software up to date.
Privacy risks stem from direct connections—your IP address and other network details may be exposed to peers. Use secure router settings at home, consider relay services when needed, and only communicate with trusted parties.
Financial risks are especially relevant in P2P fiat trades: always verify recipient accounts and confirm funds before releasing crypto assets. Gate’s escrow mechanism reduces risk but remain vigilant against phishing links and fake screenshots during chat and transfer steps; follow platform dispute procedures as necessary.
How Can You Experience a P2P System Firsthand?
Step 1: Run a blockchain node. Install Bitcoin or Ethereum node software on your computer to connect to the P2P network and sync blocks—this lets you observe how transactions and blocks propagate.
Step 2: Try decentralized content distribution. Install an IPFS desktop client, publish a small file to the network, then retrieve it from another device to see how nodes fetch data using distributed indexing.
Step 3: Conduct peer-to-peer fiat trading. Use Gate’s P2P fiat module to select merchants or individuals, review order terms, complete payment, and receive crypto assets under escrow protection—experience direct matching combined with platform safeguards.
Step 4: Manage your network environment. Check router ports and NAT settings; enable port forwarding or use relay solutions as needed to improve connection stability in P2P systems.
What Are the Trends in P2P System Development?
P2P systems are advancing toward higher performance and stronger privacy. Modern network layers employ faster protocols (such as UDP enhancements or QUIC) for quicker message propagation; privacy improvements include encrypted handshakes and anonymous routing to reduce exposure of network details.
In blockchain networks, node counts and geographic distribution continue to grow. According to Bitnodes, visible Bitcoin nodes numbered around 15,000 as of mid-2024 (Source: Bitnodes, June 2024), with numbers fluctuating over time and conditions. More projects now use modular network stacks and pluggable P2P libraries (like libp2p) to suit different consensus mechanisms and resource constraints.
Key Takeaways of P2P Systems
P2P systems connect participants directly without a central server, forming the backbone of decentralized applications like blockchains. They achieve data synchronization through node discovery and message propagation, offering superior fault tolerance and open participation. Effective use requires combining platform-level escrow and security practices to manage network and financial risks. As protocols and privacy technologies evolve, P2P systems will strike better balances between performance, availability, and regulatory compliance.
FAQ
What Is the Difference Between P2P Communication and P2P Downloading?
Both use P2P architecture but serve distinct purposes. P2P communication means two devices exchange messages directly (e.g., instant messaging), while P2P downloading pulls file data simultaneously from multiple users' computers. In blockchain networks, P2P primarily enables communication—nodes sync ledger data—yet both modes adhere to the core principle of decentralization.
Why Must Blockchain Use a P2P Architecture?
Blockchain requires decentralized operation without a central server. The P2P model lets each node equally store data, verify transactions, and broadcast information; thus, no single node failure can crash the entire network. In contrast, if a client-server system’s server is attacked or shut down, the whole system could collapse.
What Are the Requirements to Join a P2P Network?
You need appropriate wallet or node software (such as the Bitcoin client), a stable internet connection, and sufficient storage space. On Gate’s platform, you can connect to blockchain’s P2P network via wallet features. Regular users don’t need complex configurations—the wallet software automatically discovers other nodes for you.
Is Having More Nodes in a P2P Network Always Better?
More nodes mean greater security and decentralization but also increased verification latency. Bitcoin has tens of thousands of nodes for high security but slower transaction confirmation; Ethereum also has many nodes but uses light clients to ease device requirements. Whether you run a full node or a light node depends on your device capabilities and security preferences.
Are P2P Systems Vulnerable to Hacking?
Because P2P networks lack single points of failure, they are harder to take down than centralized servers. However, individual nodes can still face DDoS attacks or interference from malicious actors. Protective measures include running up-to-date software, using firewalls, and limiting connections per node. Platforms like Gate implement robust security so users need not be overly concerned.
Related Articles

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?
